CrediX Ghosts the Web After $4.5M Hack Exit Scam, or Just Radio Silence?
CrediX Finance, once seen as a rising DeFi lending platform, is now at the center of what looks like a full-blown exit scam. The team behind the protocol has gone dark since August 4, shortly after a $4.5 million exploit rocked its ecosystem.
CrediX’s Sudden Disappearance Raises Red Flags
What started as a hack due to a compromised admin wallet quickly morphed into something sketchier. Hackers used the privileged access to mint fake tokens, drain the liquidity pools, and move funds through Sonic and Ethereum bridges all before spreading the assets across multiple wallets.
Initially, CrediX announced it struck a deal with the hacker to return funds within 48 hours in exchange for a treasury payment, and promised a full refund via airdrop. But here’s the twist: the team pulled the plug on its website, deleted its X account, and shut down its Telegram leaving users in the lurch.
Security Teams Step In
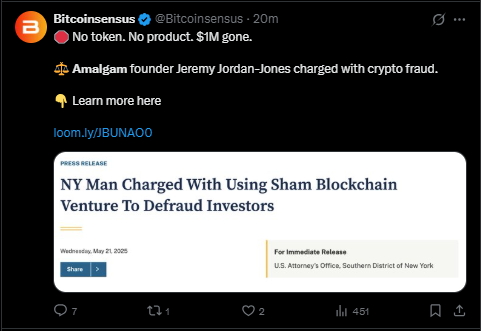
CertiK called it: this has the classic signs of an exit scam. Meanwhile, SlowMist confirmed the attacker had access to CrediX’s multisig wallet six days prior.
Stability DAO claims it has tracked two team members using KYC data and is preparing a legal report in collaboration with Euler, Trevee, Beets, and Sonic Labs. The crypto sleuthing community is now in overdrive.
YOU MIGHT ALSO LIKE: Breaking ! Ethereum Forms Bull Pennant as Daily Transactions Hit #1 Record High